This sounds really easy but it can be challenging if you have never done it before. Out of the box Windows does not want to run Powershell scripts in an automated fashion. There are some security hurdles put in place for this reason. This blog post will show you what you need to know to make Powershell task scheduling a breeze.
I am not going to go through creating a Powershell script. That is the subject of another blog post. In this post we will expect that you have a script that you are already running manually and need to schedule it using the task scheduler.
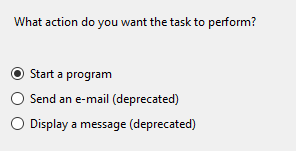
Open the Task Scheduler and configure a basic task with these parameters:

Using the –ExecutionPolicy Bypass argument allows us to bypass the script execution restrictions that all Windows operating systems have enabled by default. This is best because it does not remove the security barriers. We will just go around them when the script runs. The “Add arguements (optional): text box needs to have your script name with a “.\” proceeding it. This an execution parameter that tells Powershell to execute the name as a program or script. Finally, we need to tell the task where to look for the script. In this case it is C:\Scripts.

Yes we want to append the argument.

We still need to add some details to this script before it will run.

We need to tell the task who to run the task as. I recommend using an account that has local admin rights that is not an account named Administrator. If you decide you don’t want to use a local Administrator account, you must choose an account that has the “Log on as a batch job” user right in the local security policy. Click “Run whether or not the user is logged on or not” and check the box that says “Run with the highest privileges”.
Click OK. Then if prompted, enter the credentials of the account being used to run the script.
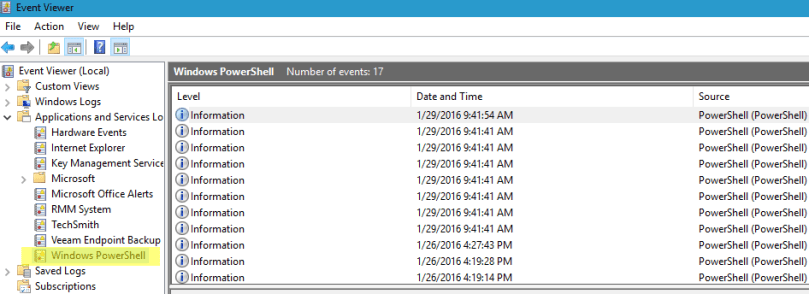
That should be all you need. If you have trouble, make sure you look into the Event logs for clues as to what is going wrong. Powershell has its own event log trap. Find it here:
Happy Powershelling!
Nice post! Thanks for sharing amazing content.
LikeLike
Thanks!
LikeLike